Новое видео
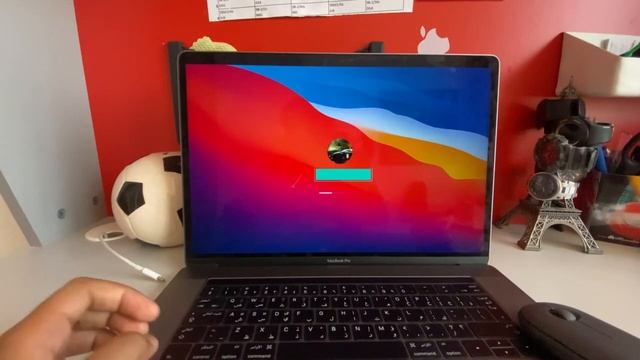
A Deep Dive into macOS MDM and How it can be Compromised
Видео: A Deep Dive into macOS MDM and How it can be Compromised
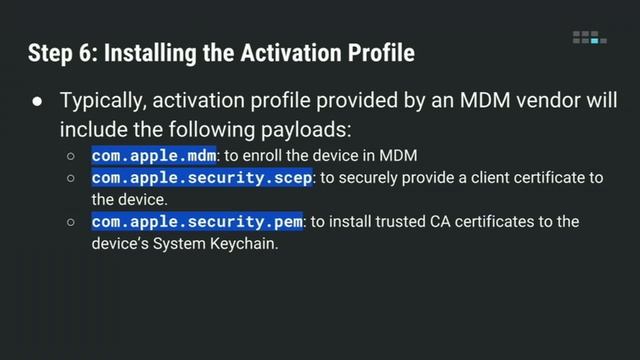
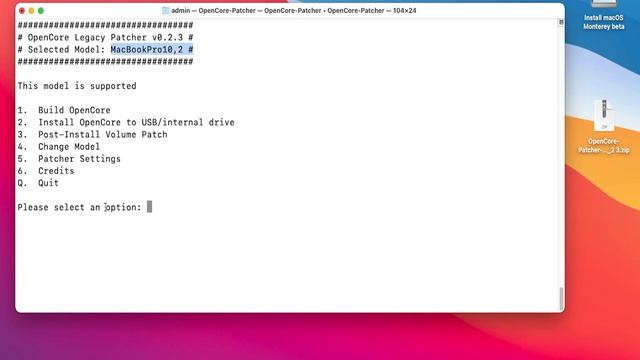
Our talk walks through the various stages of bootstrapping showing which binaries are involved the IPC flows on the device and evaluates the network TLS security of key clientserver communications. We will follow with a live demo showing how a nation-state actor could exploit this vulnerability such that a user could unwrap a brand new Mac and the attacker could root it out of the box the first time it connects to WiFi. By Jesse Endahl Max Bélanger Full abstract and materials: a-deep-dive-into-macos-mdm-and-how-it-can-be-compromised-11674,
Комментарии ( 0
)
Сначала новые
Сначала старые
Сначала лучшие
Загружено по ссылке
Присоединяйтесь к обсуждению
М
Гость
М
Гость
Я не совсем поняла, что хотели добится организаторы этой акции, когда закопали на ГОД машины? Хотели сравнить какая больше проржавеет? Земля, да еще и с водой, для любого металла это однозначно смерть, тем более за такой не малый срок. Мне, если честно, очень жаль как машины, так и людей, смотрет...
М
Гость
М
Гость
Канадские дома и технологии их строительства. Плюсы и минусы SIP панелей. Как построить дом из СИП панелей. ... Поэтому на наших просторах строительство часто называют канадским (как и сами дома). Но часто такие объекты путают с каркасно-щитовыми. Принципиальное различие в том, что канадские дома...
М
Гость
2024-02-21 в 04:54:36
2026-04-22 в 03:37:08
2024-02-21 в 04:14:37
2024-02-21 в 05:24:56

![ЯПОНИЯ ЗАКРУЧИВАЕТ ГАЙКИ [get.gt]](https://pic.rtbcdn.ru/video/2026-04-22/27/8e/278ea8b0d23953f60f15f7c7df98e09b.jpg)